The Importance of VAPT Services in Modern Businesses
As businesses move to digital platforms, cybersecurity has become essential. Organizations now manage large volumes of sensitive data, increasing their exposure to cyber threats.
VAPT (Vulnerability Assessment and Penetration Testing) helps businesses identify, assess, and address security weaknesses before they can be exploited.
What is VAPT?
Vulnerability Assessment and Penetration Testing (VAPT) is a comprehensive method for evaluating the security of systems, networks, and applications.
- Vulnerability Assessment (VA):
Identifies security flaws, misconfigurations, and system weaknesses.
- Penetration Testing (PT):
Simulates cyberattacks to exploit vulnerabilities and assess their impact.
Together, VAPT offers a comprehensive view of your organization’s security posture, highlighting both vulnerabilities and their severity.
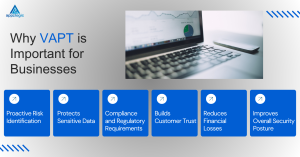
Why VAPT is Important for Businesses
- Cyber threats are constantly evolving. VAPT enables businesses to identify vulnerabilities before attackers can exploit them.
- Businesses manage critical data, from customer information to financial records. VAPT helps keep this data secure from breaches and leaks.
- Many industries require security testing to meet compliance standards (ISO, GDPR, PCI-DSS). VAPT supports organizations in fulfilling these obligations.
- Security breaches can harm your reputation. Demonstrating strong security practices builds trust with customers and stakeholders.
- A single cyberattack can result in significant financial losses. Early detection through VAPT reduces the risk of costly breaches and downtime.
- VAPT not only identifies issues but also provides actionable insights to strengthen your systems.
 Key Challenges Businesses Face Without VAPT
Key Challenges Businesses Face Without VAPT
- Hackers now use advanced tools, automation, and AI-driven attacks, rendering traditional security measures insufficient.
- Many organizations lack awareness of hidden vulnerabilities in their applications, APIs, or infrastructure.
- Modern systems often include cloud, on-premises, hybrid, and third-party integrations, which complicate security management.
- Without regular testing, vulnerabilities may go undetected until a breach occurs.
- Failure to meet security standards can result in penalties, legal issues, and lost business opportunities.
- Many companies lack in-house security experts, which makes continuous monitoring and testing challenging.
Common Areas Covered in VAPT
- Web Applications
- Mobile Applications
- APIs and Integrations
- Cloud Infrastructure
- Network Security
- IoT Devices
Any of these areas can serve as entry points for attackers if not properly secured.
How VAPT Works
- Understand the system and identify potential entry points.
- Detect known vulnerabilities using specialized tools.
- Simulate attacks to assess real-world impact.
- Prioritize vulnerabilities based on severity.
- Provide a detailed report with findings and recommended remediation steps.
- Confirm that vulnerabilities have been properly addressed.
Best Practices for Effective VAPT
- Conduct VAPT regularly, such as quarterly or after major updates.
- Use both automated tools and manual testing.
- Prioritize addressing critical vulnerabilities.
- Integrate VAPT into the development lifecycle, including DevSecOps practices.
- Engage experienced cybersecurity professionals.
Conclusion
In today’s digital-first world, cybersecurity threats are inevitable, but breaches are not. VAPT services give businesses the visibility, insights, and protection needed to remain secure.
By identifying vulnerabilities early and addressing them proactively, organizations can protect their data, maintain compliance, and build lasting trust with customers.
Investing in VAPT is not only about security; it also ensures business continuity and resilience in an increasingly connected world.
By partnering with experts like Appzlogic, organizations can identify vulnerabilities and build a resilient, secure digital infrastructure.
Frequently Asked Questions
Ideally, VAPT should be performed at least once every quarter or after major system updates.
Vulnerability assessment identifies issues, while penetration testing exploits them to assess real-world risk.
Yes, small businesses are often targeted due to weaker security, making VAPT equally important.
No system is 100% secure, but VAPT significantly reduces risks and improves security posture.
It depends on the system size and complexity, but typically ranges from a few days to a few weeks.