AI-Driven Phishing: One of the Top Identity Threats for 2026
Introduction
As cyber threats escalate rapidly, AI-driven phishing attacks are rapidly becoming one of the most immediate and significant identity threats in 2026. Unlike older phishing emails, which were often easy to spot, these new AI-powered scams now use advanced technologies to create highly personalized, automated attacks that can bypass even the most sophisticated security systems. Understanding how AI-powered cyberattacks work is essential for businesses and individuals to act now and defend themselves before it’s too late. Before delving further, let’s clarify what AI-driven phishing entails and why it poses such a major risk.
About AI-Driven Phishing?
This attack leverages machine learning and artificial intelligence tools to craft extremely convincing phishing messages by rapidly analyzing vast amounts of data. Cybercriminals deploy Natural Language Processing (NLP) to precisely mimic writing styles, generate deep-fake audio or video impersonations, and automate massive campaigns with alarming success rates. Attackers can now tailor their messages based on social media, emails, and other public information—making every attempt dangerously authentic and trustworthy. Given these sophisticated tactics, it’s essential to understand why AI-driven phishing poses a major threat in 2026.
AI-Driven Phishing is a Major Threat in 2026
AI support enables analysis of diverse data sources to craft tailored phishing emails that feel authentic, greatly raising the risk of identity theft and making Business Email Compromise (BEC) and deepfake attacks more effective.
AI can replicate the communication styles of executives or colleagues, increasing the effectiveness of social engineering attacks such as BEC.
AI-generated deep-fake audio and video impersonations make fraud more credible and difficult to detect.
AI enables cybercriminals to launch thousands of phishing attempts simultaneously, increasing the reach and impact of these threats. Recognizing the variety of attack methods is crucial for effective defense.
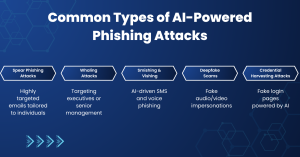
Common Types of AI-Powered Phishing Attacks
- Spear Phishing Attacks require highly targeted emails, custom-designed for individuals, and using personalized information to appear valid and increase the chances of success.
- Whaling Attacks focus on high-level executives or senior management, exploiting their authority and access to sensitive business data.
- Smishing & Vishing use AI-driven techniques to provide phishing attacks through SMS messages and voice calls, making them more convincing and harder to detect.
- Deepfake Scams support AI to create realistic fake audio or video impersonations, enabling attackers to mimic trusted individuals.
- Credential Harvesting Attacks involve AI-powered fake login pages designed to trick users into entering sensitive information such as usernames and passwords.
An increase in AI-driven cyber threats has affected most businesses and individual fronts. Many are facing financial losses due to fraud, data breaches, loss of sensitive information, reputational damage, and compromised user identities. In 2026, it is important to have a strong cybersecurity strategy. With these risks in mind, let’s examine practical steps to protect against them.
The following points highlight how to protect against AI-driven phishing.
- To detect suspicious patterns and abnormalities, it is useful to implement Advanced Email Security.
- Training employees in phishing attack prevention and identifying suspicious communications.
- An extra layer of security is added to protect against unauthorized access, even if credentials are lost.
- A Zero Trust approach should be adopted, where every request is verified before access is granted.
- Incident Response (IR) readiness assessments and compromise assessments are conducted to identify vulnerabilities. As threats evolve, organizations must also consider how cybersecurity will continue to adapt in the age of AI.
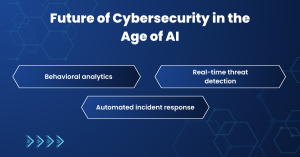
Future of Cybersecurity in the Age of AI
As AI-driven threats grow more sophisticated and inevitable, organizations must urgently implement AI-driven cybersecurity solutions. The future now relies on:
- Behavioral Analytics monitors user activity patterns to detect unusual behavior, helping identify potential threats before they escalate.
- Real-Time Threat Detection continuously analyzes network activity and system data to instantly identify and respond to cyber threats as they occur.
- Automated Incident Response uses intelligent systems to quickly contain and mitigate security incidents, reducing response time and minimizing potential damage.
Staying ahead demands relentless monitoring and immediate, proactive defense strategies to avoid devastating consequences. As we anticipate future developments, these efforts will be critical to maintaining cybersecurity resilience.
Conclusion
The rise of AI-driven phishing is a critical cybersecurity challenge that cannot be ignored. In 2026, the unprecedented growth in identity threats demands urgent and decisive action. To defend their digital future, businesses must prioritize advanced cybersecurity solutions, ongoing employee training, and proactive threat monitoring. Vigilance, adaptation, and commitment to innovation are essential to stay ahead of attackers and protect valuable digital assets.
Frequently Asked Questions
AI-driven phishing is a type of cyberattack in which hackers use Artificial Intelligence (AI) to create highly personalized, realistic phishing messages. These attacks often mimic trusted sources, making them harder to detect than traditional phishing.
In 2026, AI-powered cyberattacks are more advanced due to automation, personalization, and deepfake technology. This makes identity theft and data breaches more frequent and difficult to prevent.